Calculating clear-cut network segmentation ROI can be tricky. It is a preventive investment, a vaccination against cyberattacks. Thinking it is unnecessary? Or waiting until it is too late?
Why is network segmentation required?
Many businesses have an IT architecture based on systems designed during a politically stable era. Frequently the architecture has grown over the years while getting current information on e.g. electricity consumption, ordering 24/7 services or teleworking has become standard. The result is that SCADA systems, business systems and the web are interconnected. Therefore, it is difficult to know how many paths lead to critical information. Only when dedicated tests are carried out through a risk and safety analysis all loopholes can be detected.
However, it is neither practical nor economically justifiable to protect all information in the same way. To safeguard critical information, strict network segmentation must be applied, combining physical separation with logical separation.
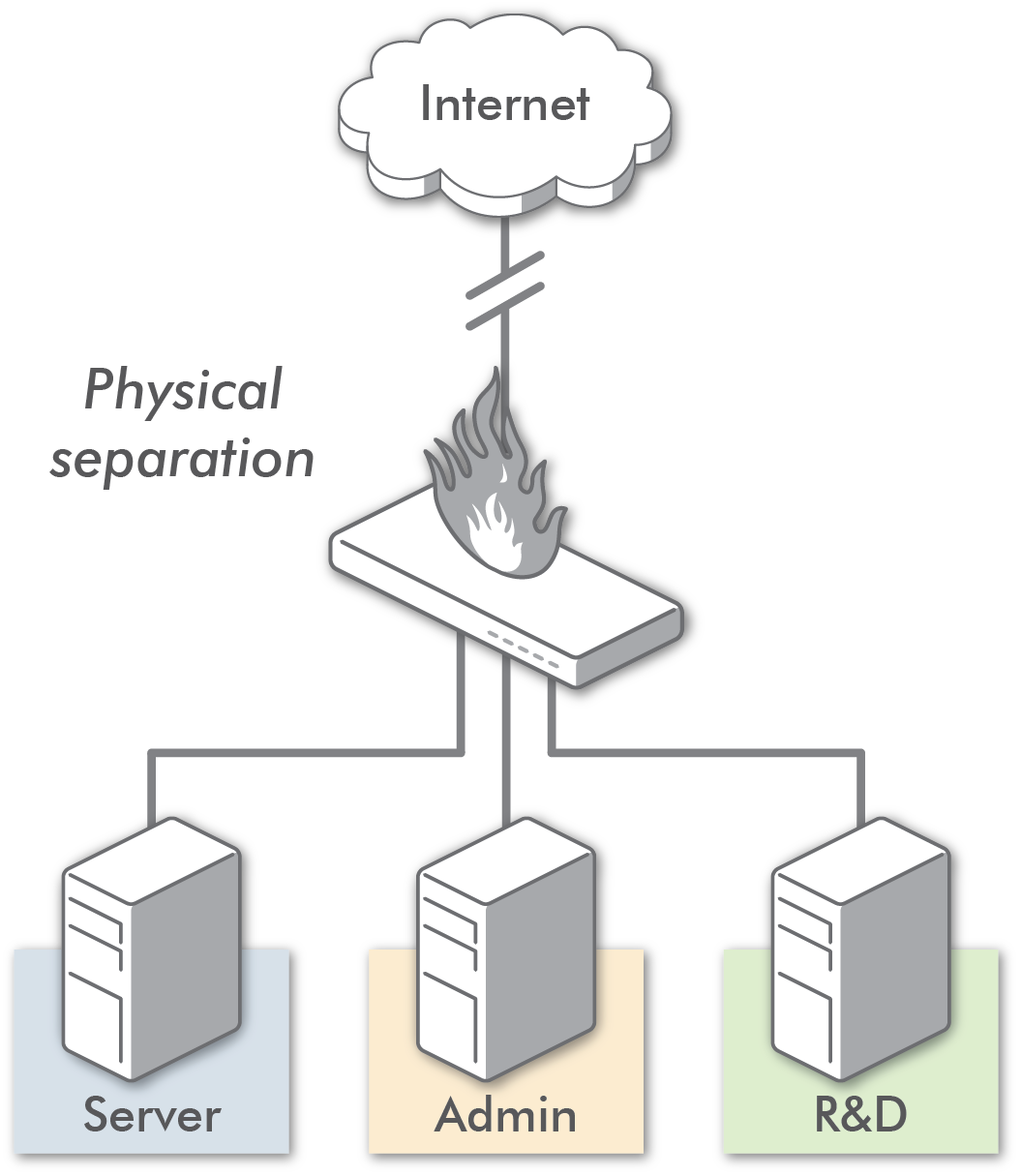
Where is physical separation vital?
Critical information requires physical separation. Simply put, an isolated island is created without connection to the outside world. This minimizes the risk area – the attacker has to sit at the computer containing the critical information.
Physical separation is very effective, but to work today a controlled exchange of information has to be possible without compromising isolation. This requires certified solutions that meet military standards, thus guaranteeing function and safety.
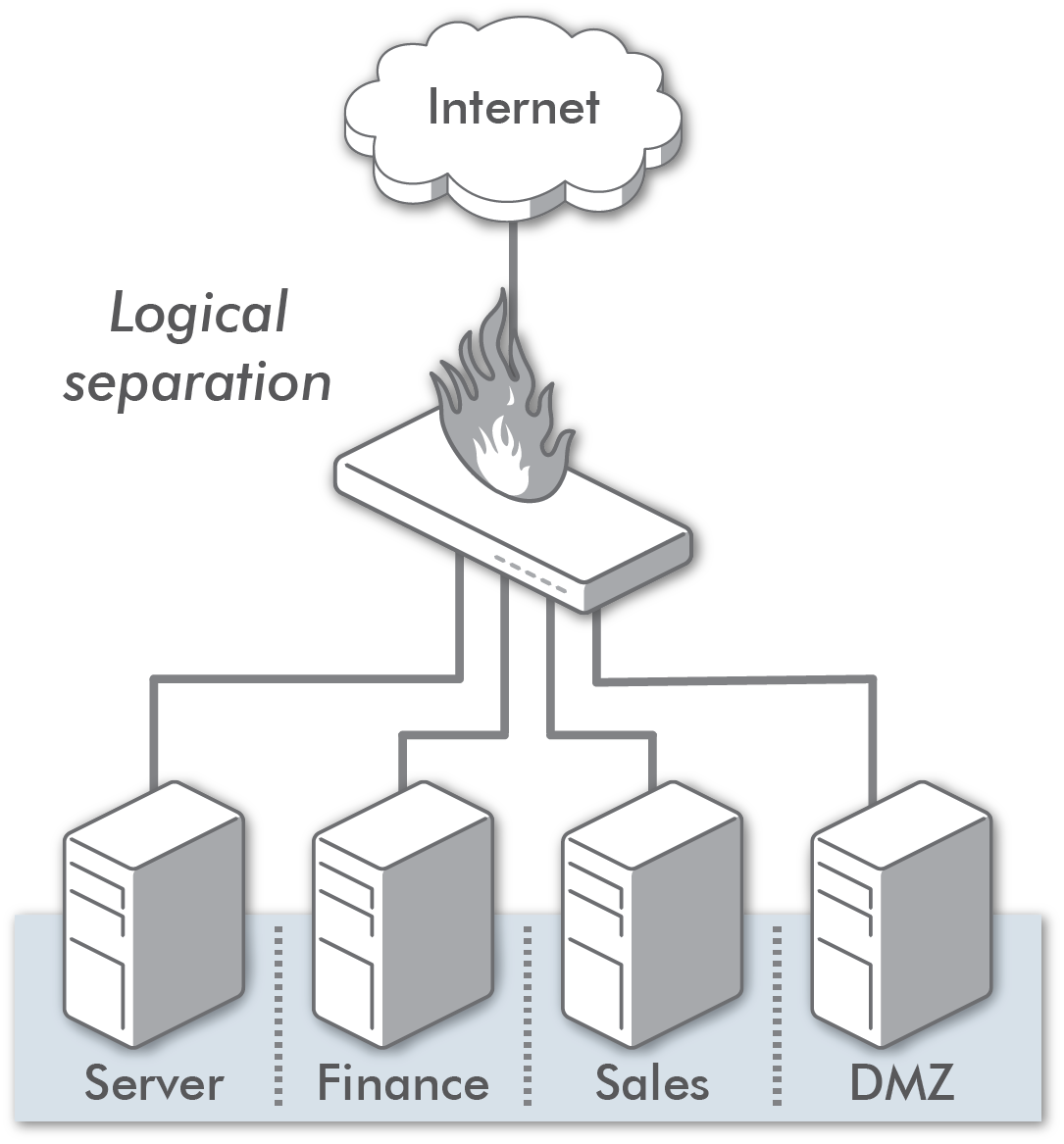
Where is logical separation appropriate?
Everywhere besides protecting critical information. Office networks should use logical separation. Different parts of the business create their own zones – finance, marketing, sales, customer service, etc. – each with different authority. As a co-worker, you access only what you need to do your job, i.e. relevant documents, not the entire folder structure.
Logical separation works as fortress’ ring-walls making it difficult for attackers to penetrate the mass of the system and infiltrate the entire IT architecture. Security is achieved with products that reduce the risk area, thus limiting cyber attack damages.
Are firewalls enough?
Today’s firewalls cannot separate administration with data flow, making them susceptible to attacks. And few firewalls offer high assurance. Entire batches could be manipulated, and when installed they expose attack points.
Additionally, when firewalls are managed through cloud services, outsourcing further increases risk exposure.
Firewalls should be used for their intended purpose: as excellent exterior protection. For logical separation, different firewalls should be used, supplemented by a protocol that requires several people to approve changes and understand the consequences of switching firewalls on or off.
When can firewalls be managed through cloud services?
For office networks with limited access to critical information, cloud services are a cost-effective and good solution.
Important advice
Involve management to identify critical information and the real threats to it. Apply a combination of logical and physical separation – from a safety point of view, this is always recommended.



